Seven years is an eternity in technology.
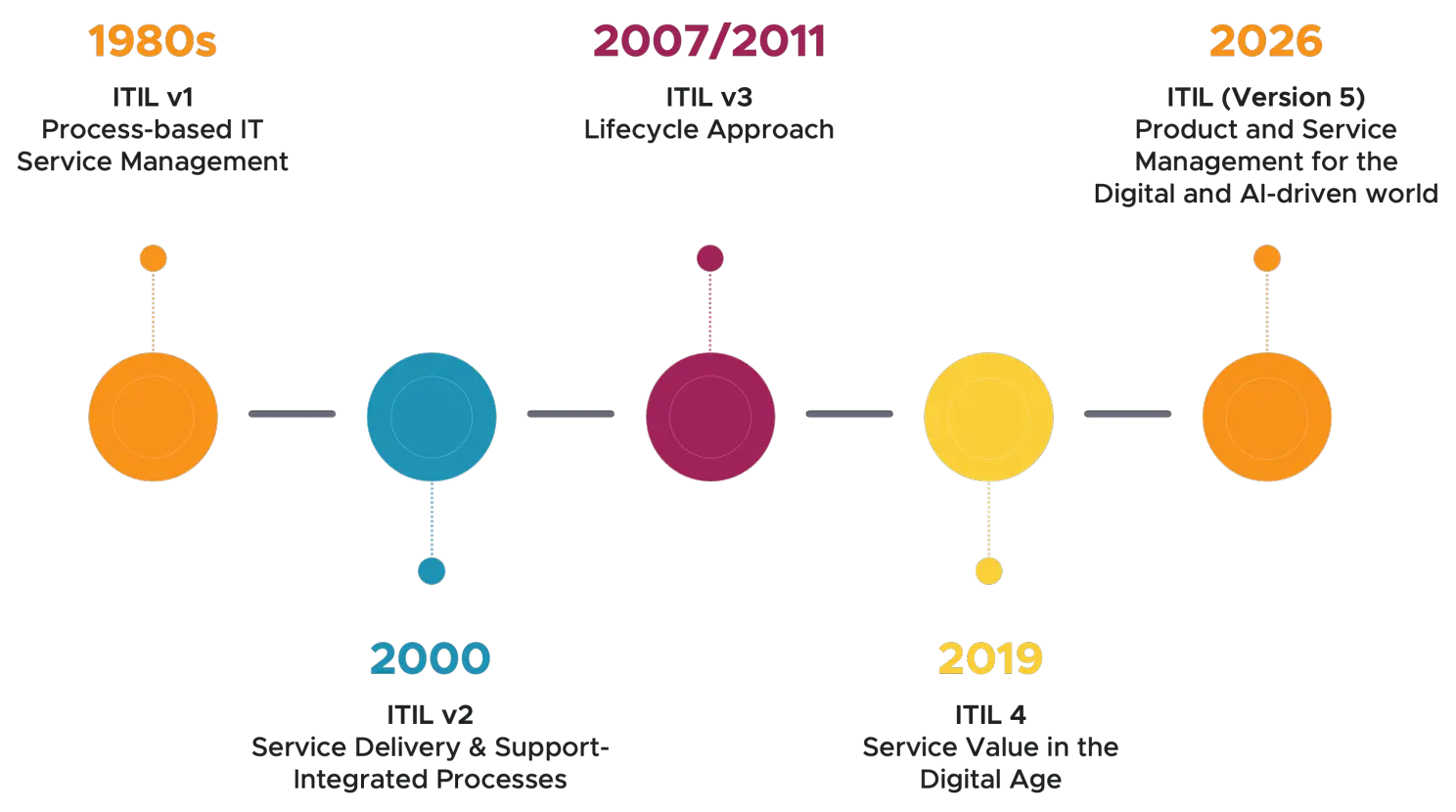
When ITIL 4 was released in early 2019, cloud computing was still something many organizations were “moving toward.” Agile and DevOps were aspirational buzzwords rather than embedded operating models. Artificial intelligence was interesting, promising, and mostly experimental. Digital transformation was something companies talked about in strategy decks rather than something they had lived through.
Fast forward to today, and the world looks very different.
Cloud computing is no longer “new.” It is the default. Automation has crept into nearly every corner of the workplace. Digital products and digital services now dominate entire industries. Customers expect near-instant gratification, minimal defects, and continuous improvement, often without ever speaking to a human being. And AI, which once felt immature and inaccessible, has become surprisingly effective, broadly available, and impossible to ignore.
Against that backdrop, ITIL (version 5) feels not only reasonable, but necessary.
This is not a radical reinvention of ITIL. Nor is it a repudiation of ITIL 4 or previous versions. Instead, ITIL v5 represents a measured, thoughtful evolution, one that recognizes a changed world and the existing digital ecosystem, acknowledges where some organizations are today, and perhaps more importantly, where many need to be if they hope to thrive or even survive.
At its core, the new ITIL is grappling with a more existential question than previous versions:
What is the role of humans in a service economy increasingly shaped by automation, AI, and digital products?
To understand ITIL (version 5), we first need to understand what happened between ITIL 4 and now.
In 2019, cloud adoption was still uneven. Many organizations were experimenting with Infrastructure as a Service (IaaS), cautiously piloting Software as a Service (SaaS), and debating whether Platform as a Service (PaaS) was worth the risk.
Today, cloud is not a strategy. It is infrastructure. Organizations no longer ask if they should move to the cloud. They ask how much, how fast, and how safely. The conversation has shifted from adoption to optimization, cost control, resilience, and vendor dependency.
Cloud normalized the idea that you may own the product, but you rent the service. You might buy a phone, but you subscribe to the ecosystem. You might install an application, but the value is delivered continuously through updates, analytics, integrations, and experience design.
This shift alone fundamentally changed service management.
Automation is no longer limited to infrastructure provisioning or scripted workflows. It now lives in:
Many organizations are “automated” without ever having declared an automation strategy. The result is real gains in efficiency, but also new risks, blind spots, and dependencies.
The challenge is no longer simply how to automate. It is how to govern, trust, and improve automation without losing accountability.
ITIL v5 squarely acknowledges this reality.
In 2019, digital transformation was often framed as a future state. Today, it is something organizations have survived, sometimes successfully and sometimes painfully.
Some organizations transformed parts of their business. Others created digital “sidecars” while legacy IT continued to run the engine room. Many ended up with bi-modal or dual-pace IT, where traditional systems of record coexist uneasily with high-velocity digital systems of engagement.
Very few organizations did this perfectly. This tension is not a failure. It is the lived reality for many organizations. ITIL (version 5) does not pretend otherwise.
Agile and DevOps are now widely adopted, at least in concept, but still poorly understood.
Most organizations use them somewhere. Fewer use them well. Many struggle to reconcile high-velocity development with governance, risk, and operational stability.
ITIL 4 made a significant effort to align with Agile, Lean, and DevOps. The new ITIL continues that effort, but places it in a broader organizational and human context.
Perhaps the most profound shift has been in customer expectations.
Customers no longer expect:
They do expect:
They are increasingly comfortable interacting with chatbots, as long as those bots actually solve problems. This shift alone has reshaped service desks, customer support models, and experience design. (For more on this, see our article on the Responsive Automation Center.)
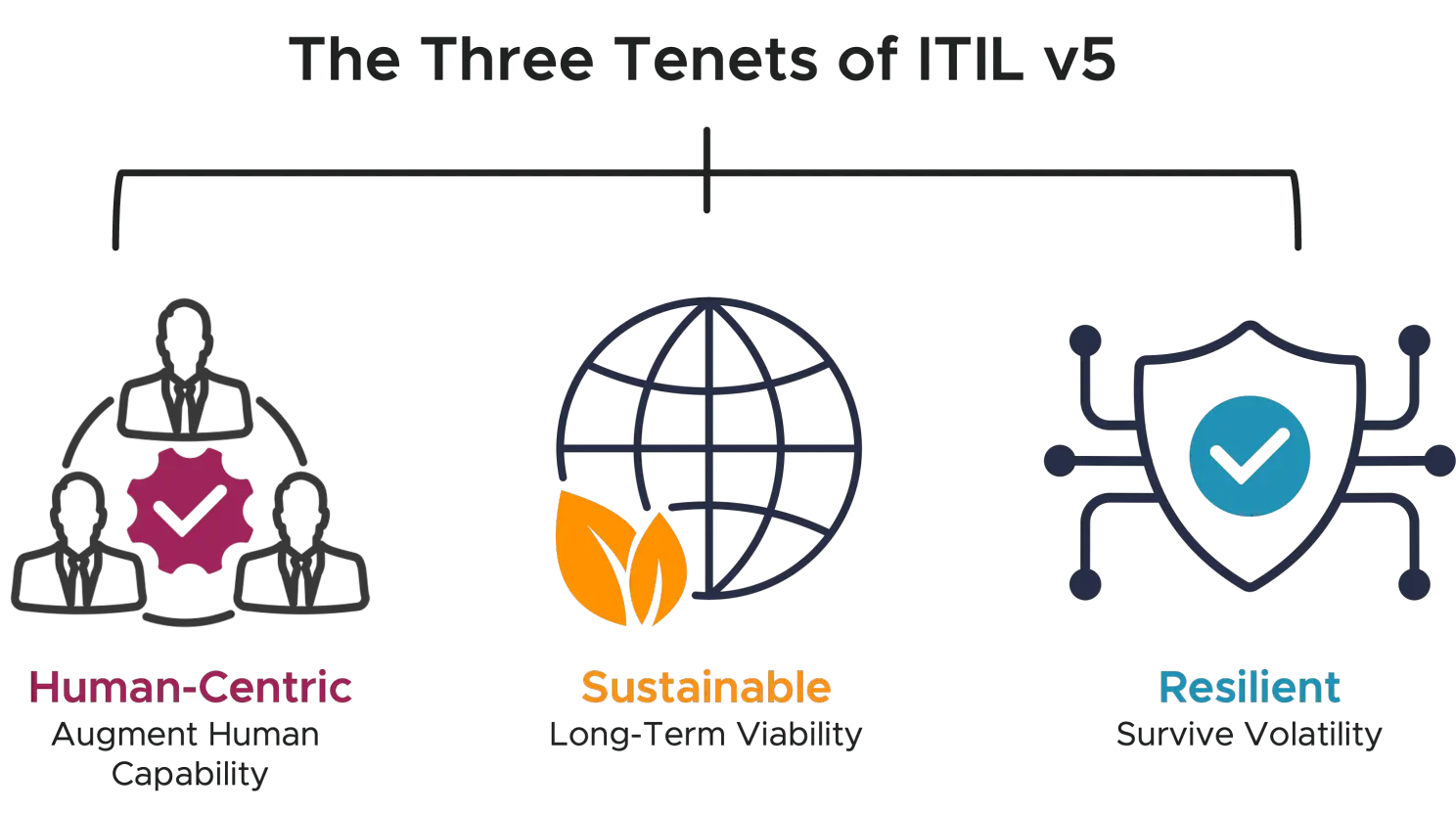
Many practitioners interpret ITIL (version 5) through the lens of Industry 5.0, a shift in emphasis from pure automation to human and technology collaboration.
Where Industry 4.0 emphasized:
Industry 5.0 asks a different question:
How do humans and advanced technology work together, rather than compete with each other?

ITILv5 frames this world around three core tenets:
Despite the philosophical shift, some key aspects of ITIL 4 remain intact.
The ITIL Guiding Principles are a set of universal recommendations that help organizations make sound decisions, prioritize actions, and navigate complexity, regardless of where they are in their improvement journey. Rather than prescribing specific processes or structures, the guiding principles provide practical direction that can be applied to any initiative, from digital transformation to day-to-day operational decisions.
The seven ITIL Guiding Principles are still present in the new ITIL, and still relevant. What changes is the emphasis on how they work together.
In practice, organizations sometimes cherry-pick guiding principles and treat them as isolated slogans. That approach tends to fail. ITIL (version 5) leans into the idea that these principles form a system, not a menu.
The Four Dimensions provide a holistic view of what must be considered to design, deliver, and improve services effectively. The four dimensions (Organizations and People, Information and Technology, Partners and Suppliers, and Value Streams and Processes) ensure that services are not viewed in isolation or through a single lens. By considering all four dimensions together, organizations reduce the risk of siloed decision-making and increase their ability to create value that is balanced, resilient, and sustainable.
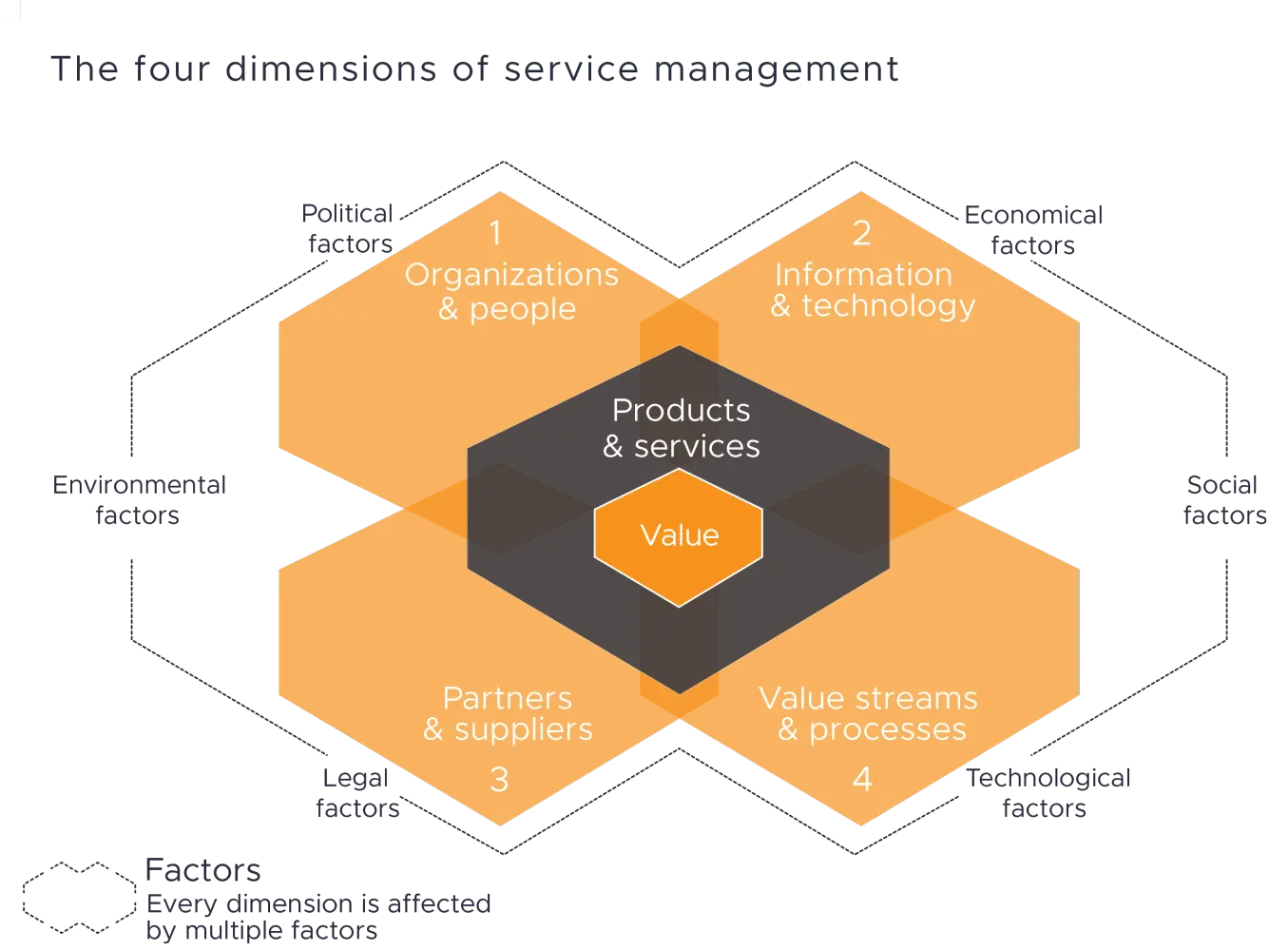
The Four Dimensions remain, but their definitions have evolved to better reflect digital ecosystems, product thinking, and human factors.
ITIL v5 also goes into more depth on organizational culture, how it shapes the organization, and how leaders can influence it.
Organizations that still treat these dimensions as a checklist rather than a balancing act will continue to struggle.
The Service Value System (SVS) describes how all components and activities of an organization work together to facilitate value creation through services. It provides an integrated operating model that connects guiding principles, governance, the service value chain, practices, and continual improvement into a cohesive system.
In ITIL (version 5), the SVS remains central, with renewed focus on digital governance.
Governance in the new ITIL is not about control for its own sake. It is about ensuring that digital capability evolves responsibly, transparently, and in alignment with organizational values.
One of the most important contributions of ITIL v5 is its explicit framing of People + AI. This is not a framework obsessed with replacing humans. Instead, it recognizes that:
ITIL (version 5) positions AI as a collaborator, not a usurper.
Safety Culture was introduced in ITIL 4, but ITIL (version 5) calls it out more explicitly and expands on it. In ITIL v5, Safety Culture is about creating environments where people:
This is not about eliminating failure. It is about preventing fear from becoming the dominant operating model.
Automation failures, biased algorithms, fragile systems, and runaway technical debt all have real-world consequences. Without Safety Culture, continuous improvement collapses into risk avoidance. The new ITIL explicitly acknowledges the need for psychological, operational, and systemic safety.
ITIL (version 5) draws a clearer distinction between digital products (what is built) and digital services (how value is consumed). This matters because many organizations still manage digital products like projects and treat digital services like afterthoughts.
In addition to digital products and services, ITIL v5 introduces lifecycle activities that reflect modern product management:
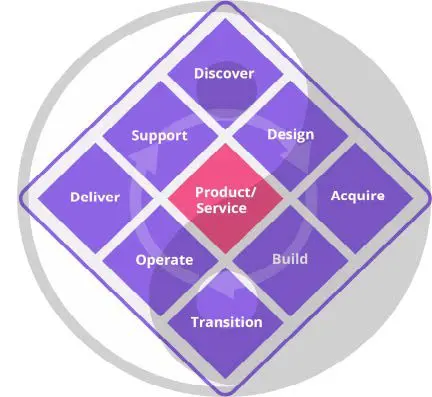
This lifecycle acknowledges that value creation does not stop at deployment, and that operations and support are not secondary concerns.
A service economy is a model in which value is created primarily through the delivery, consumption, and continual improvement of services rather than through the ownership of physical products. Customers pay for access, outcomes, and experiences, often enabled by digital technology, while value is co-created over time through ongoing interaction between providers, consumers, and supporting ecosystems.
In a service economy:
ITIL (version 5) leans fully into this reality.
Borrowing from ITIL 4’s Drive Stakeholder Value, the new ITIL formalizes and expands upon the service journey. The service journey is how stakeholders move from need to outcome across touchpoints and interactions.
Site Reliability Engineering (SRE) is a discipline that applies software engineering principles to the design, operation, and improvement of reliable and scalable services. Its focus is ensuring systems meet defined reliability, availability, and performance targets. SRE is explicitly discussed in ITIL v5, acknowledging its growing influence in modern operations.
Value stream mapping is a technique used to visualize, analyze, and improve the end-to-end flow of activities required to co-create value with a customer or stakeholder. It identifies how work moves across people, processes, technology, and organizational boundaries, highlighting delays, handoffs, waste, and bottlenecks that impede value creation.
Although introduced in ITIL 4, value stream mapping is no longer optional. In digital environments, understanding flow is essential to improving speed, quality, and resilience.
Interestingly, ITIL (version 5) de-emphasizes practices, at least in the core text. Incident Management, Change Enablement, and Release Management still receive attention, but the framework avoids turning practices into the center of gravity.
Practices are still important. They help achieve larger organizational goals and use resources effectively. But practices can become silos. Organizations that obsess over practices often miss the bigger picture.
(Note: A comprehensive practice reference exists in the Appendix of the ITIL (version 5) Foundation book for those who need it.)
If you have taken ITIL 4 Foundation, ITIL v5 Foundation will feel familiar.
The exam focuses more on understanding concepts and relationships than memorizing definitions.
As with ITIL 4, ITIL (version 5) retains a three-pronged certification structure designed to support different career paths and organizational roles. While the architecture will feel familiar to experienced practitioners, most of the courses within each path are new, reflecting the evolution of service management toward digital products, digital services, experience, and transformation.
At the foundation of every path is ITIL (version 5) Foundation, which establishes a common language, core concepts, and an understanding of the service economy, digital value creation, and the role of humans and technology working together.
From there, candidates may pursue one or more of the three advanced certification pillars.
If you already hold ITIL 4 Foundation, you do not need to retake Foundation to move forward. ITIL 4 Foundation is fully recognized as a prerequisite for all advanced qualifications in the new ITIL.
PeopleCert has also shared that ITIL 4 and ITIL (Version 5) are expected to run in parallel for a minimum of 12 months. That parallel runway is designed to give individuals and organizations time to complete in-flight learning journeys while the new ITIL rolls out.
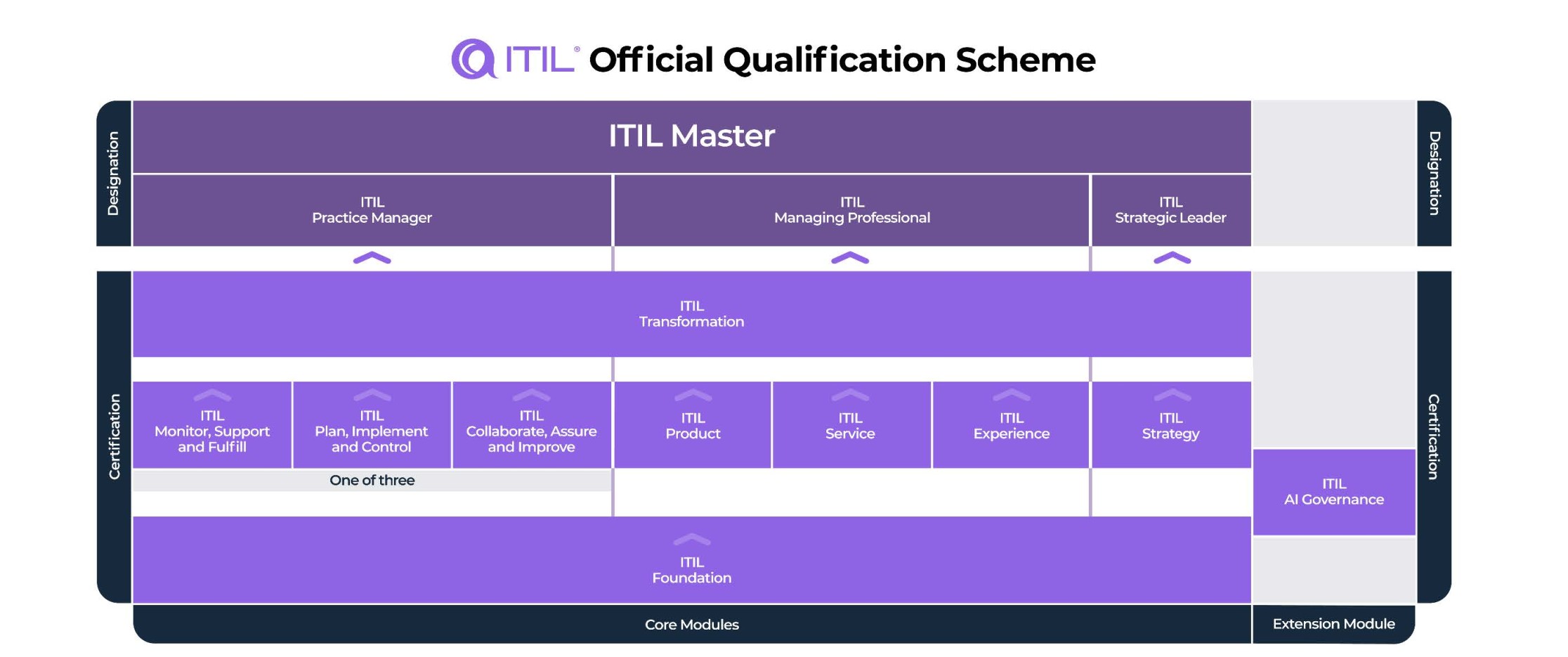
The ITIL Managing Professional path is designed for practitioners, managers, and leaders responsible for the end-to-end delivery and management of digital products and services.
To achieve the Managing Professional designation, candidates must complete:
This path emphasizes practical application, operational excellence, product and service lifecycle management, and the delivery of consistent, high-quality experiences in modern digital environments.
The ITIL Strategic Leader path focuses on strategy, governance, and organizational transformation, recognizing that service management is no longer confined to IT but is a core business capability.
To achieve the Strategic Leader designation, candidates must complete:
This path is well-suited for senior leaders, executives, and transformation sponsors who shape organizational direction and ensure digital initiatives align with long-term business, societal, and sustainability goals.
The ITIL Practice Manager path is intended for professionals who own, manage, and continually improve service management practices and operational capabilities.
To achieve the Practice Manager designation, candidates must complete:
This path provides depth in practice execution while maintaining alignment with broader organizational and transformation objectives.
ITIL Transformation is required across all three certification paths. It serves as a unifying capstone that brings together strategy, practices, products, services, and experience into a cohesive view of how organizations evolve, adapt, and remain resilient in a digital, service-based economy.
Professionals who achieve all three designations:
automatically earn the prestigious designation of ITIL Master.
The ITIL Master designation recognizes individuals who possess comprehensive, end-to-end mastery of ITIL (version 5), from strategic leadership and transformation to operational execution and continual improvement.
ITIL (version 5) is not just for entry-level IT support, nor is it solely for IT practitioners.
It is for leaders who want to remain relevant.
Technology is no longer a back-office concern. It shapes how work is done, how value is delivered, and how organizations compete. Leaders who treat technology as someone else’s problem risk being replaced, not by AI, but by people who know how to use it better.
The bar for humans has been raised.
ITIL v5 offers a lens through which leaders can:
Here is my candid assessment of ITIL (version 5), based on having been part of the ITIL journey since ITIL v3, having co-authored an ITIL 4 publication, and most of all, client experience:
In that sense, ITIL v5 is partially aspirational. Aspiration is not a flaw, as long as we recognize it as such.
Other frameworks such as VeriSM, IT4IT, and integratedITSM have emerged with good intentions, and they have value. But none of them has meaningfully displaced ITIL.
They are typically:
Adjacent frameworks like Agile, DevOps, PMBOK, PRINCE2, and SIAM remain valuable, but complementary. The new ITIL does not attempt to replace them. It provides a common language and conceptual backbone.
Like it or not, ITIL remains the gravitational center of IT service management.
ITIL (version 5) is not perfect. No framework is. But it represents a reasonable evolution, one that acknowledges a changed world, embraces digital reality, and places humans back at the center of the conversation.
In an era obsessed with efficiency, ITIL v5 dares to ask whether efficiency alone is enough.
If Industry 5.0 is about anything, it is about ensuring that you and I, the humans, still matter.
And that may be the most important service of all.